Ever needed to work from home, but have the problem of using a Samba share on the server while at work, but not at home? Well here is a simple fix.
In my example I’m working on a “sandbox” from home. The folders I work in have files with more than one owner. This becomes a nightmare even when I ssh in. Some might think an NFS share would be better. Unfortunately with NFS you are stuck with the current file permissions. With Samba those file permissions are given to you. That may sound a bit confusing, so let me try to clear it up a bit. Let us say there is only one file in the Samba share. User “ender” has ownership of the file. I can’t alter it. When I login with Samba the file appears to be owned by me not “ender”. Now I can do my work and when I log out the file is still owned by “ender”… wow, I don’t think I did a good job there either. Lets just say that when in comes to file permissions, Samba is the way to go.
But I need to work over ssh? Only port 22 is open from the outside. No problem!
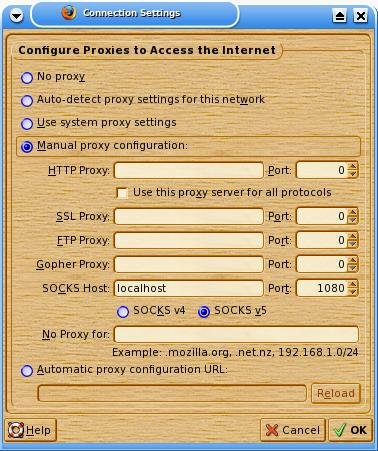
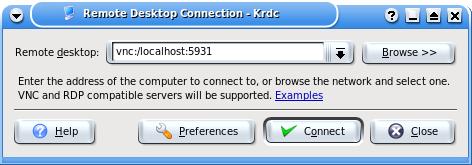
We simply need to create a ssh tunnel. For this we already know we need to connect to port 139 on “sandbox”, and we need a local port to connect to. I would say just make it 139 also. Unfortunately for me I’m also running Samba on my local machine, and I can’t do that. So any non used port will do. How about 1139?
ssh user@remotehost -L 1139:localhost:139 |
ssh user@remotehost -L 1139:localhost:139
Simple as that. That will connect port 1139 on your local machine to 139 of the remote host. The “localhost” actually refers to the remote host. It’s saying connect 1139 to my local machine to the remote host’s “localhost” port 139. If you are actually connecting to a windows box on that network you can “bounce” off the linux host to the windows. For more information you can refer to a previous post: Secure VNC for free for more information.
Now comes the fun part. You have 1139 on your local machine tied to 139 on the server. Now to mount the share as a local disk.
As root we mount the share.
mount -t cifs //sandbox/www /mnt/sandbox/ -o username=<username>,password=<password>,ip=127.0.0.1,port=1139,uid=<your local UID>,gid=<your local GID>,file_mode=0770,dir_mode=0770 |
mount -t cifs //sandbox/www /mnt/sandbox/ -o username=<username>,password=<password>,ip=127.0.0.1,port=1139,uid=<your local UID>,gid=<your local GID>,file_mode=0770,dir_mode=0770
Fill in your Samba share’s username and password, then your local machine’s UID and GID. To find the UID and GID type:
cat /etc/passwd | grep <your local username>
cat /etc/group | grep users |
cat /etc/passwd | grep <your local username>
cat /etc/group | grep users
This assumes your regular user is part of the “users” group.
It will show 2 numbers. UID is most likely 500 or 1000, and GID is likely to be 100.
After filling in the blanks hit enter and your set! This will use the local port 1139 through the ssh connection to 139 on the server. It may seem a little slow at first, but that may be from the old server I’m connecting to.
If you want to store the info in fstab try:
//sandbox/www /mnt/sandbox cifs noauto,rw,username=<username>,password=<password>,ip=127.0.0.1,port=1139,uid=<UID>,gid=<GID>,file_mode=0770,dir_mode=0770 0 0 |
//sandbox/www /mnt/sandbox cifs noauto,rw,username=<username>,password=<password>,ip=127.0.0.1,port=1139,uid=<UID>,gid=<GID>,file_mode=0770,dir_mode=0770 0 0
Now for some reason I can’t quite get this to work, but others seem to have no problem with it. You can add the mount line above into your /etc/fstab file so a regular user can mount. I did this, but it doesn’t work for me. I get an error saying “only ROOT can mount this”. If you get this error try:
chmod +s /usr/sbin/mount.cifs
chmod +s /usr/sbin/umount.cifs |
chmod +s /usr/sbin/mount.cifs
chmod +s /usr/sbin/umount.cifs
Like I said, it didn’t work for me, however after creating the ssh tunnel I simply open a new terminal window, su to root and then type “mount //sandbox/www” and it works fine.
Also, the reason I don’t background the ssh connection is because if it drops you may run into some problems with trying to mount it again (or even trying to use umount). I had this problem and it gave me a head ache to try to fix it without just rebooting. I’m sure I could have forced an umount.cifs, but I didn’t try (actually I didn’t realize it was actually still mounted). When logging in I recommend running a command that continuously sends data like “top”. That will help prevent the connection from being lost. If the connection is lost you must umount the share, reform the ssh tunnel, and try again.
NOTE: If you are connecting to a share on a Windows 7 box you must open 2 ports, 139 and 443 (or so I’m told). To do this open up a few terminal windows and create two separate connections. After that I do not know as I have never tried.
EDIT NOTE: I wrote this some time ago and just now got around to posting it. I hope everything works fine for you as the mount works fine for me (except under fstab for some reason). Don’t forget that by typing the command into the shell it will be stored in your history. If the password is sensitive I would recommend clearing out your history after mounting the share.